Wow you found three different articles, all about the same CVE, that the manufacture published a firmware patch for before any public disclosure was made. That’s definitely just as bad as pretending you don’t know about CVEs in your products lol.
borari
Cybersecurity professional with an interest in networking, and beginning to delve into binary exploitation and reverse engineering.
- 0 Posts
- 23 Comments
You presented one that doesn’t have security vulnerabilities? Here’s yet another CVE out for trendnet: https://nvd.nist.gov/vuln/detail/CVE-2018-19239
Every. Single. Brand. Has. CVEs. I’ve used Mikrotik, I’ve used Cisco, I’ve used Juniper, I’ve used Ubiquiti. I have a trendnet Poe switch in my attic powering some cameras and an AP right now. I have no “problem” with any brand of anything.
I do have a problem with you implying that a company doesn’t take security seriously when they do. I start to think you’re intentionally lying when you lift up trendnet as the model, because they have quite an especially atrocious history of it.
https://www.rapid7.com/db/modules/exploit/linux/misc/cisco_ios_xe_rce/
We can go back and forth on RCEs literally all day. If your bar for using a product is “no RCEs”, get off the grid entirely my guy.
MikroTik is just as serious a network company as Cisco or Juniper, and vastly more serious from an enterprise networking point of view than trendnet.
Also where tf did OP mention anything about warranties?
Edit - https://medium.com/tenable-techblog/trendnet-ac2600-rce-via-wan-8926b29908a4
Edit - https://www.archcloudlabs.com/projects/trendnet-731br/
Edit - lol holy removed look how customer focused trendnet is! They just plugged their ears and pretended an unauthenticated RCE in their product didn’t exist haha. https://arstechnica.com/information-technology/2015/04/no-patch-for-remote-code-execution-bug-in-d-link-and-trendnet-routers/
Edit - oof yikes look there’s more. https://www.nccgroup.com/us/research-blog/technical-advisory-multiple-vulnerabilities-in-trendnet-tew-831dr-wifi-router-cve-2022-30325-cve-2022-30326-cve-2022-30327-cve-2022-30328-cve-2022-30329/
You are a foolish person.
Yeah I’ve worked at WISPs that were pushing TBs through their core routers every day. Those core routers? Mikrotiks. Every apartment buildings core routers and fiber aggregation switches? Mikrotiks. You had to get down to the access layer switches that fed the individual apartments to hit Cisco equipment.
This person is just repeating some removed they read somewhere, hoping it makes them sound knowledgeable. In another post they’re recommending trendnet removed. Get back to me when you can set up BGP peering on your trendnet lol.
I can’t quite get a read on if you’re being sarcastic or not, but if you are you should know that there are curated porn blocklists for pihole. This obviously won’t stop anyone from accessing porn via nsfw channels on sites that are not exclusively nsfw, like lemmy, Reddit, tumblr, or whatever.
Run pihole with a MikroTik router at your houses demarc.
Set up firewall rules in the tik to redirect any packet with dst tcp/udp 53 outbound on wan to the pihole. If you’re worried about dns when pihole is down, create disabled rules to allow the dns traffic as well, then set up a scheduler script using if blocks to toggle the sets of rules depending on status. This will force any client on your network, even one with hardcoded dns IPs, to use the pihole.
If the client is configured for DoH you’ll just have to build out an ip block list in the MikroTik and block all known DoH IPs.
Create firewall rules to drop all vpn traffic you can, combining port based rules and similar IP lists as for DoH, but subbing in VPN provider IPs. If you want to route your home traffic over a vpn, set up a vpn client in the router itself and basically site-to-site your home to the vpn provider you use.
This would block the vast majority of kids trying to bypass parents blocks, but it’s asking quite a lot from the parents who don’t have experience configuring this stuff already.

 121·8 days ago
121·8 days agoThe illegal goods on telegram aren’t piracy related.

 41·17 days ago
41·17 days agoIf someone starting swatting the extended family of local police chiefs I’d be willing to bet that even the police unions would be calling for an end to these types of raids, regardless of how they were handled.

 19·19 days ago
19·19 days agoOh man, Ingress was such a better game. I got slightly obsessed with it for a year or two. I had my entire state covered for a couple of days, before one of the nodes or whatever was broken.

 1·2 months ago
1·2 months agoI wouldn’t buy a used MacBook from an individual seller unless I could meet in person to verify there’s no BIOS/TPM lock going on that would prevent me from doing a secure erase and wiping the SSD to start fresh. A laptop with a replaceable ssd is probably less of an issue, but I’d still feel more comfortable having a picture of the BIOS showing no password set or anything, and a picture of it booted to desktop at minimum so you know it isn’t a stolen laptop that has a password no one knows. If you’re buying from like a second hand recycler or something, anyone that sells through significant volume of devices, I’d be much more comfortable just pulling the trigger sight unseen.
Yes, treating crypto as a way to invest is a scam. The vast majority of crypto and crypto-adjacent “projects” are scams.
We live in a world where payment providers have the power to force Etsy to delist vendors that sell sex toys to customers of a legal age, payment apps like Venmo or PayPal will permaban your account for selling NSFW art or products, and physical cash is being largely abandoned for cards and digital wallets. Surely you can see the benefits of a completely anonymous payment method?
To be clear, I vastly prefer cash, but there’s an obvious issue with trying to anonymously use cash to pay for something on the internet or to send money to someone who isn’t within easy driving distance.
Slam an Edge user agent up in there.
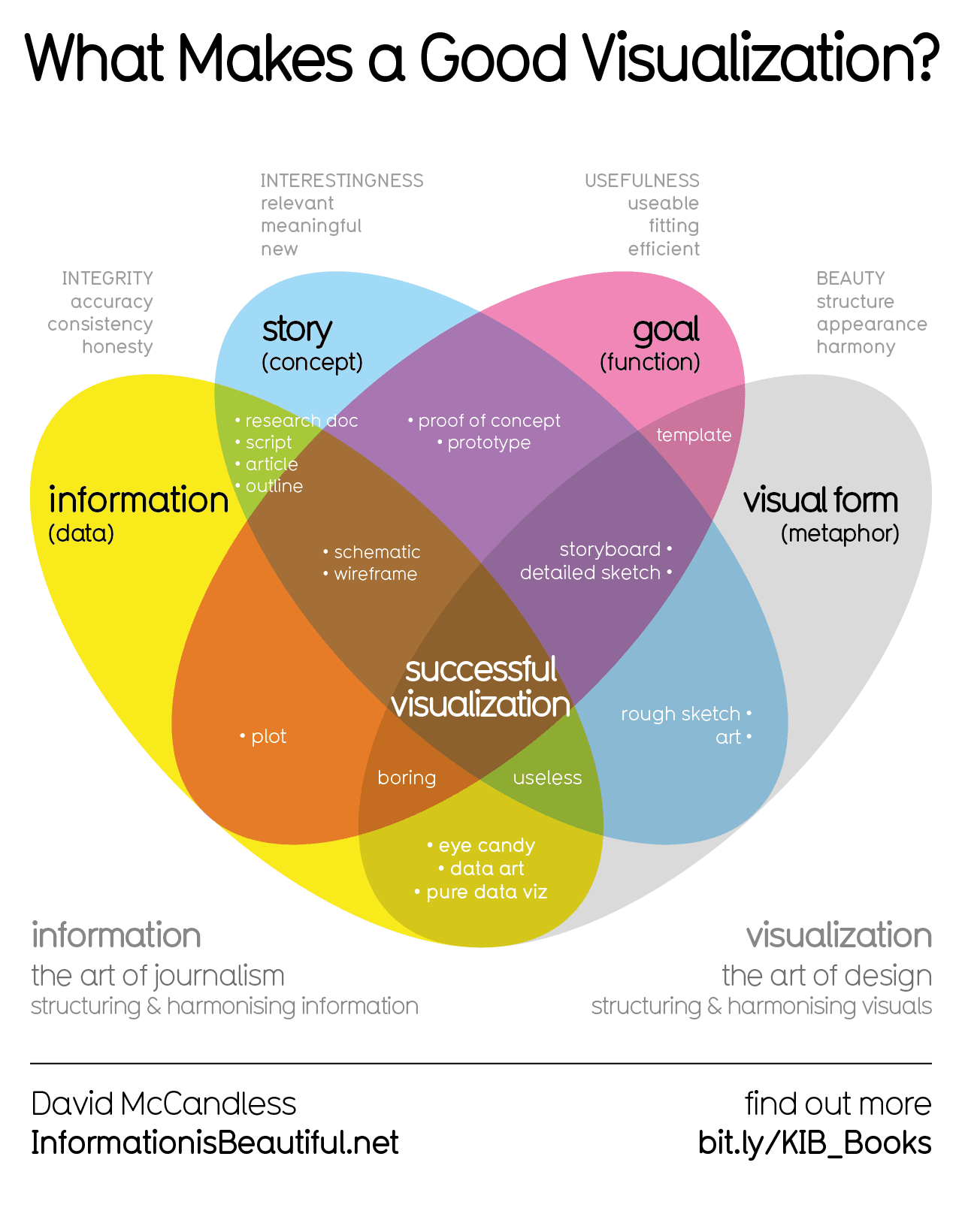
I think the intent of the big green bar in the middle is to signify that all the revenue streams combine to form this single total revenue, then the various cost centers chip away at it until you get the singular green revenue total in the bottom left.
I guess it’s how our brains are wired like another poster said, because I definitely didn’t pick up an implied relationship between the revenue and costs here.
Just to note, Kali is a downstream release of Debian Testing, not Ubuntu. Also for question 55 you didn’t include “git clone and build binary from src”.

 172·5 months ago
172·5 months agoyour autocorrect misspelled debian server in that last line there.

My dude. You are not a serious person. I’m blocking you so I don’t waste my time with you in the future. Enjoy your life I guess.